All articles
-

Silicon Retirement: Evaluating Enterprise Hardware for Secondary Markets vs. Material Recovery
-
The False Positive Epidemic: Protecting Your Content ROI in the Era of Algorithmic Scrutiny
-
The Silent Conversion Killer: Why Brand Voice is the Ultimate Casualty of the AI Era (And How to Fix It)
-

Why Modern Software Engineering Teams are Building with Cloud-Based Number Pools
-
How Refurbished Hardware Helps Businesses Reduce Costs and E-Waste
-
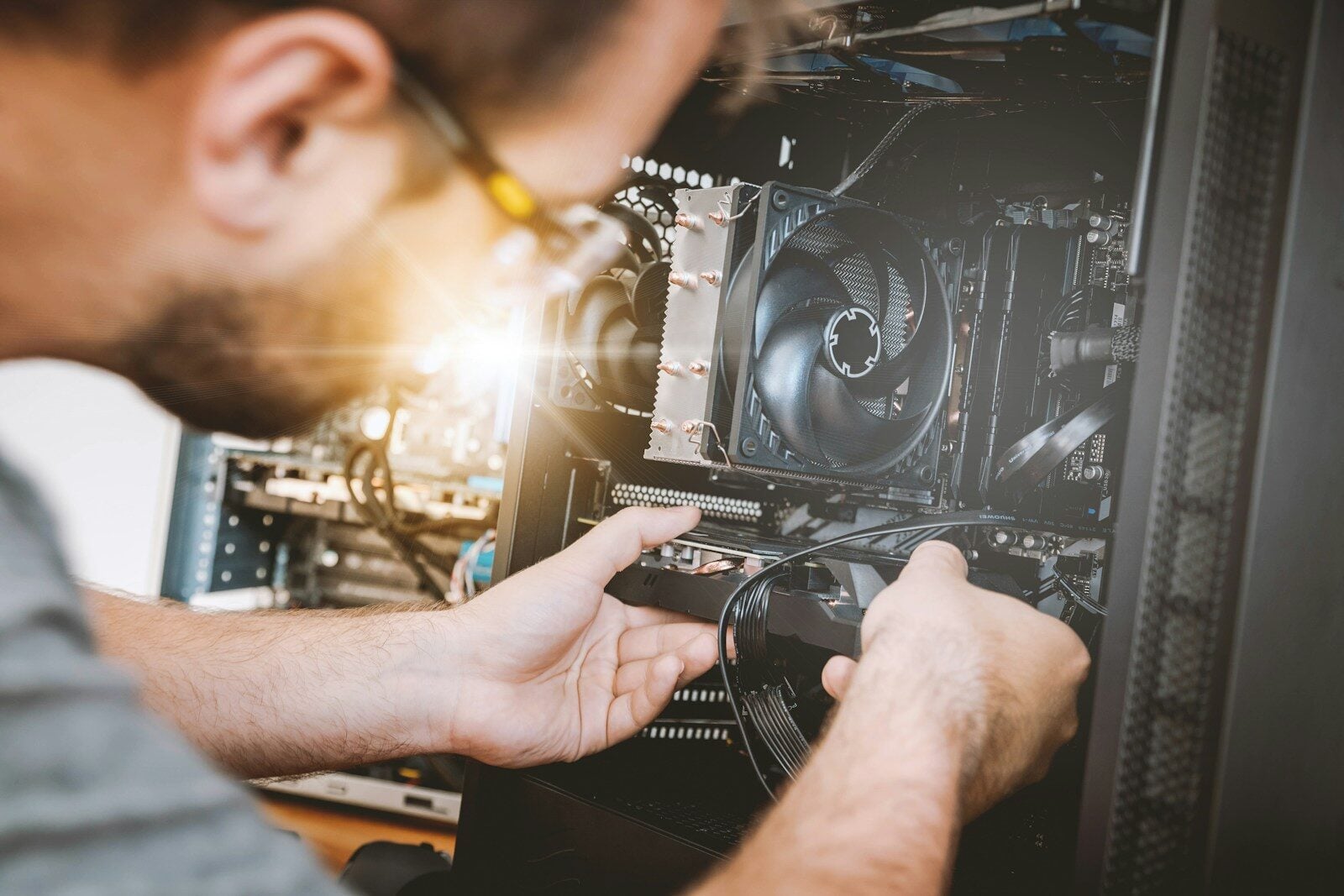
Gaming PC Optimization for YouTube Content Creation
-

Top Customer Feedback Management Tools in 2026
-

Semrush One: 7 SEO Platforms That Help You Show Up in ChatGPT, Gemini, and Google AI
